As security enthusiasts, we are constantly pursuing more knowledge of our field. Anytime a new class of vulnerabilities (or even simply a new exploit) surfaces, we are eager to dissect it to figure out how it works, as well as what measures we can take to protect against it. We know that the best way to learn is by doing, for example, by setting up two machines and using one to emulate an attacker and one to emulate the victim. This approach works well, and provides useful, practical information. However, it is not cost or space effective, since one must have two machines to create this scenario, and this approach is also very time consuming since one must re-build the victim OS every time it is breached by the "attacker" in order to have a fresh-start. What we as security hobbyists need is a solution to these problems that allows us to cheaply and easily build isolated machines on the fly with which we are free to experiment without fear of breaking something.
Enter virtualization. By utilizing virtualization software, we are able to create virtual machines (VMs) that act independently of our host operating system, allowing us to essentially create an entire operating system within our existing operating system. An example of this would be running an Ubuntu Server distribution VM on a Windows 7 host OS. We would have complete isolated access to each of these operating systems as if they were on two physically separate machines. Having this solution available allows us to cheaply create, rebuild, and destroy VMs as we see fit in order to practice exploitation execution and prevention without putting our host operating system at risk.
Available Virtualization Software
There are many different virtualization software solutions from which one can pick when choosing to create a virtual lab. Three products that are widely known and used are VMWare, Citrix, and VirtualBox. In this blog, I will show you how to create a lab using VirtualBox since it is open-source (free!), and allows you to create and run multiple VMs at one time using a centralized interface (something other solutions provide, but at a cost). Although, while we use VirtualBox in this post, I encourage you to research the other solutions and find which best suits your needs!
Getting Started with VirtualBox
VirtualBox is an open-source virtualization solution provided by Oracle. It is a free product, and is licensed under the terms of the GNU General Public License (GPL) version 2. To get started building a virtual lab, download the VirtualBox version that corresponds to your host operating system. Then, refer to the Installation Guide for instructions on how to install VirtualBox.
Got it installed? Good deal. Now let's create a virtual lab.
Creating the Virtual Lab
We will begin creating our virtual lab by first creating a virtual machine. In this post, we will create two machines: a BackTrack5 R1 VM and an Ubuntu Server 11.10 VM. It should be noted that it doesn't matter what OS you choose to use on your VM's. This post will simply show you how to create an isolated virtual lab in which you can practice exploitation on boxes you control.
So let's get started creating the machines. First, you will need to download the images to use when creating the virtual machines. For this post, we will download the images in iso form. Then, you will need to open VirtualBox, and choose to create a "New" virtual machine.
Then, click "Next" through the "Create a New Virtual Machine Wizard" to get to the screen in which you can name your VM, and select the OS Type. For both the BackTrack and the Ubuntu VM, select "Linux" for the Operating System, and "Ubuntu" for the Version.
Next, we have to select how much Memory (RAM) we want to allocate to the Virtual Machine. As you will see in the wizard, the recommended base size is 512 MB, which is what I recommend when building a new VM. You can always adjust this value later.
In the next screen, you will select whether or not you wish to use an existing virtual hard disk, or create a new one. In this post, we will create a new virtual hard disk.
Then, since we chose to create a new virtual drive, we need to select the format in which we want to save it. There are four formats available, each with their own uses. Since in this post we assume that we won't need to export our VM's to other virtual appliance software, we will use the VirtualBox-specific VDI format.
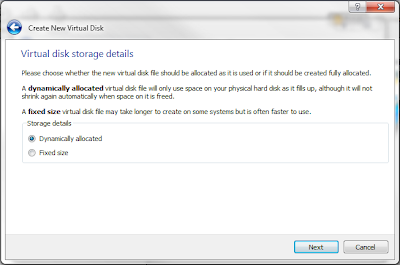
We will then choose to dynamically allocate virtual hard drive space for our VM. This will allow the actual physical space on our hard drive to be used more conservatively - only being allocated as needed.
Next, we choose what to name the VDI file, and where to put it, and we also select the maximum allotted physical space for the VM. In this post, we will allocate the recommended 8 GB for the machine.
Available Virtualization Software
There are many different virtualization software solutions from which one can pick when choosing to create a virtual lab. Three products that are widely known and used are VMWare, Citrix, and VirtualBox. In this blog, I will show you how to create a lab using VirtualBox since it is open-source (free!), and allows you to create and run multiple VMs at one time using a centralized interface (something other solutions provide, but at a cost). Although, while we use VirtualBox in this post, I encourage you to research the other solutions and find which best suits your needs!
Getting Started with VirtualBox
VirtualBox is an open-source virtualization solution provided by Oracle. It is a free product, and is licensed under the terms of the GNU General Public License (GPL) version 2. To get started building a virtual lab, download the VirtualBox version that corresponds to your host operating system. Then, refer to the Installation Guide for instructions on how to install VirtualBox.
Got it installed? Good deal. Now let's create a virtual lab.
Creating the Virtual Lab
We will begin creating our virtual lab by first creating a virtual machine. In this post, we will create two machines: a BackTrack5 R1 VM and an Ubuntu Server 11.10 VM. It should be noted that it doesn't matter what OS you choose to use on your VM's. This post will simply show you how to create an isolated virtual lab in which you can practice exploitation on boxes you control.
So let's get started creating the machines. First, you will need to download the images to use when creating the virtual machines. For this post, we will download the images in iso form. Then, you will need to open VirtualBox, and choose to create a "New" virtual machine.
Then, click "Next" through the "Create a New Virtual Machine Wizard" to get to the screen in which you can name your VM, and select the OS Type. For both the BackTrack and the Ubuntu VM, select "Linux" for the Operating System, and "Ubuntu" for the Version.
Next, we have to select how much Memory (RAM) we want to allocate to the Virtual Machine. As you will see in the wizard, the recommended base size is 512 MB, which is what I recommend when building a new VM. You can always adjust this value later.
In the next screen, you will select whether or not you wish to use an existing virtual hard disk, or create a new one. In this post, we will create a new virtual hard disk.
Then, since we chose to create a new virtual drive, we need to select the format in which we want to save it. There are four formats available, each with their own uses. Since in this post we assume that we won't need to export our VM's to other virtual appliance software, we will use the VirtualBox-specific VDI format.
We will then choose to dynamically allocate virtual hard drive space for our VM. This will allow the actual physical space on our hard drive to be used more conservatively - only being allocated as needed.
Next, we choose what to name the VDI file, and where to put it, and we also select the maximum allotted physical space for the VM. In this post, we will allocate the recommended 8 GB for the machine.
After this step, we are finished! Review the specifications and click "Create" to create the Virtual Hard Disk file. Then, review the final specs of the VM, and click "Create" again to create the actual Virtual Machine. You should be redirected back to the Home Screen, and you should see your newly created VM in the left sidebar. Double click on it to power it on.
Since this is the first time powering up the VM, you will the "First Run Wizard" appear. This wizard will help select the bootable media for your virtual machine. Simply select the iso image file you downloaded earlier, click "Next," review the specifications, and select "Start" to boot the VM from the iso.
Installing BackTrack5 R1 on the VM
Since this post would grow far too long if I showed you how to install both the Ubuntu Server and BackTrack5 R1 on the VM's, I will simply show you how to install BackTrack5 R1, and leave it as an exercise for the reader to install Ubuntu Server. In this segment, I will be following (most of) the instructions found on the BackTrack website.
Installing BackTrack is incredibly easy. Since you have selected the iso as the media from which you want to boot, after you start the VM, and the boot loading completes, you will be presented with a screen that looks like:
We want to select the "Default Boot Text Mode." Then, after this completes, you will be presented with a root shell. To start the GUI, simply type "startx."
After the GUI loads, simply double click on the "Install BackTrack" icon on the desktop, and then follow the instructions that can be found here to complete the installation of BackTrack to your virtual hard disk.
Communication is the Key
Got BackTrack5 R1 and Ubuntu Server installed? Awesome. Now it's time to set up networking between the VM's so that they can communicate, and you can practice exploiting a remote machine.
The Networking settings for a VM can be found under the "Settings" icon on the home screen after selecting a VM to which the settings will apply. Note: Most settings require that the VM is powered off before changes can be made. It is recommended that you power down the machine before making any changes.
There are 4 main types of settings to which the VM's NIC can be attached. By default (most likely to protect the machine from outside threats and still have Internet connectivity to download updates), VM's start with one NIC enabled which is NAT'd. This means that the VM essentially treats the physical hosts NIC as a router. This mode will not work for us, because each VM is isolated, and cannot talk to each other. Also, with an outbound connection to the Internet available, we do not have a truly isolated network in which we can run our tests.
While you can read about the other types of networking available for virtual NIC's in VirtualBox, we will digress and move forward with configuring Host-Only Networking.
Note: In this example, I choose to allow my VM's to connect to my physical host as well. If you are performing risky testing (such as malware analysis), you very well may not want to take this risk. If this is the case, please refer to the "Addendum: Internal Networking" section of this post below on how to set up Internal Networking instead of Host-Only Networking.
Configuring Host-Only Networking
So, what is Host-only Networking? Host-only networking creates an internal LAN that includes the VM's and the physical host. This creates a new software interface on the physical machine that controls the flow of this internal traffic. Since the VM's are not connected to a physical interface (as in Bridged mode), no outbound Internet connection is established. This is exactly what we are looking for, since the VM's can talk to each other, but they are completely isolated in their own contained network.
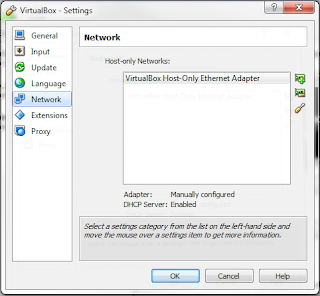
To set up host-only networking, one must first ensure that a host-only adapter is present on the physical machine, and create one if none are found. To do this, on the home-screen, select File -> Preferences. When taken to the Preferences screen, select "Network" from the left side-bar. You will be presented with a screen that looks similar to the following:
Here, you will see the list of Host-Only Adapters configured on the physical machine. You can think of each of these adapters as a virtual router that connects the physical host as well as each VM host configured to use this adapter together.
If you see a host-only adapter already listed in the main box, then select it, and check at the bottom to see if the integrated DHCP Server is Enabled. This will make your life a little simpler, since you won't have to manually configure a static IP address in the /etc/network/interfaces file on each VM. If it is not enabled and you wish to enable it, click on the wrench icon on the right hand side of the screen to configure the adapter, select the "DHCP Server" tab at the top, and check the "Enable Server" checkbox. Then, simply fill in the forms for the DHCP server settings, such as the IP Address of the server, the Subnet Mask, as well as the lower and upper bound for the dynamic addresses. An example configuration for the adapter with an IP address of 192.168.56.1 and a subnet mask of 255.255.255.0 can be seen below:
If you do not see a host-only adapter, then simply click on the top icon (with a + on it) on the right hand side of the screen to create a new adapter. Then, after the adapter has been created, click on the wrench icon on the right hand side of the screen to configure it. The default settings for IP addressing should work just fine, but you will most likely have to configure the DHCP server as shown above.
Now that you have created and configured a Host-Only adapter, you will need to configure your VM to use the settings on this adapter for its NIC. To do this, on the home-screen, select your VM in the left side bar and select the "Settings" icon on the top of the screen. Then, select "Network" on the left side of the settings window to bring up the different adapter settings configured for the VM. To allow the VM to use the Host-Only adapter, simply select the host only adapter you created from the "Attached to" drop down menu.
After you have done this for both machines, you can simply check to make sure the settings were applied by starting up the VM, and since they are both Ubuntu-based, simply typing "ifconfig" at the shell prompt will show you the IP address for each adapter. You should see an IP address that has been assigned by the host-only DHCP server. Finally, we can test communication between the two running VM's by trying to ping one from the other as shown:
Conclusion
Congratulations! You now have working BackTrack5 R1 and Ubuntu Server VM's that you can use for security testing. There are all kinds of things you can do with this setup alone. Some examples include installing old software with known exploits onto the Ubuntu machine and using BackTrack to exploit it, or trying your hand at web app exploitation by writing vulnerable web applications or downloading some pre-built vulnerable web apps and installing them onto your Ubuntu Server VM. These are good examples to get you started, but in reality you can do anything you want with a virtual setup. Just set up machines and start exploiting!
Addendum: Internal Networking
After reviewing this blog post, I have decided that it would be thorough to include a section on how to configure Internal Networking for your VM's in case you do not want your VM's to reach your physical host, and vice-versa.
By default, VirtualBox has an internal network created called "intnet" and can be found in the Network Settings for the VM (found by clicking the "Settings" icon on the home-screen). To configure this for your VM's NIC, simply change the "Attached to" property of the adapter to "Internal Network"
Then, to create a dhcp server for this internal network, open a command prompt and run the following command, changing the [bracketed] items to your desired settings:
VBoxManage.exe dhcpserver add --netname [network_name] --ip [ip_of_dhcp_server] --netmask [subnet_mask] --lowerip [lowest_ip_address_to_lease] --upperip [highest_ip_to_lease] --enable
For example, with my network name as "intnet" and me wanting to allocate 51 possible IP addresses, my command would look something like:
Then, when you start up your VM, you should see one of the provided IP addresses configured on the machine.
If you have any questions or comments, please leave them below!
-Jordan












Is there a way to add virtual switch firewall gateway etc?
ReplyDelete